It’s Time to Get Back To You.
With 24/7 Managed Security, you can unplug from nonstop alerts and get back to jam sessions with your family.
SWING BY OUR BOOTHWith 24/7 Managed Security, you can unplug from nonstop alerts and get back to jam sessions with your family.
SWING BY OUR BOOTH
Our Advanced Threat Operations Team discloses threats that shaped the cyber threat landscape in 2023.
GET YOUR COPY










THE STATE OF CYBERSECURITY
Threats are evolving, attack surfaces are expanding, and resources are shrinking. Most organizations can’t hire their way out of the problem. Managed security providers promise full coverage but only take over the most generic tasks.
Your security partner should resolve incidents quickly, strengthen your posture, and help manage your SecOps costs.
Download Our White PaperTALENT SHORTAGE
There are currently over 500k open security roles with a lack of talent to fill them.
COMPLEXITY ISSUES
The average number of security solutions an organization has deployed – speaks to the complexity issue.
BUDGET CONSTRAINTS
51% of organizations don’t have sufficient budget to meet their cybersecurity needs.
THE FUTURE OF SECOPS IS MANAGED
Building a strong security posture requires a deep understanding of your unique environment – something most MDR providers can’t do. We customize our service to you. By harnessing the speed and scalability of AI, we achieve unrivaled results.
Reduce your mean time to resolve security incidents using real-time collaboration and AI-driven automation. Eliminate noise so you can focus your efforts on what matters most.
Stay ahead of attacks with a 24/7 service that evolves as attackers do. Improve prevention through automation and get recommendations for hardening your security environment.
Get prevention, detection, and response efforts around your unique risk profile. Our experts execute, measure, and optimize your day-to-day SecOps, allowing your team to focus on critical security tasks.
THE NEW STANDARD
Our AI-powered platform and cyber defense center are at the core of everything we do. We deliver greater efficiencies, continuous protection, and faster response times.
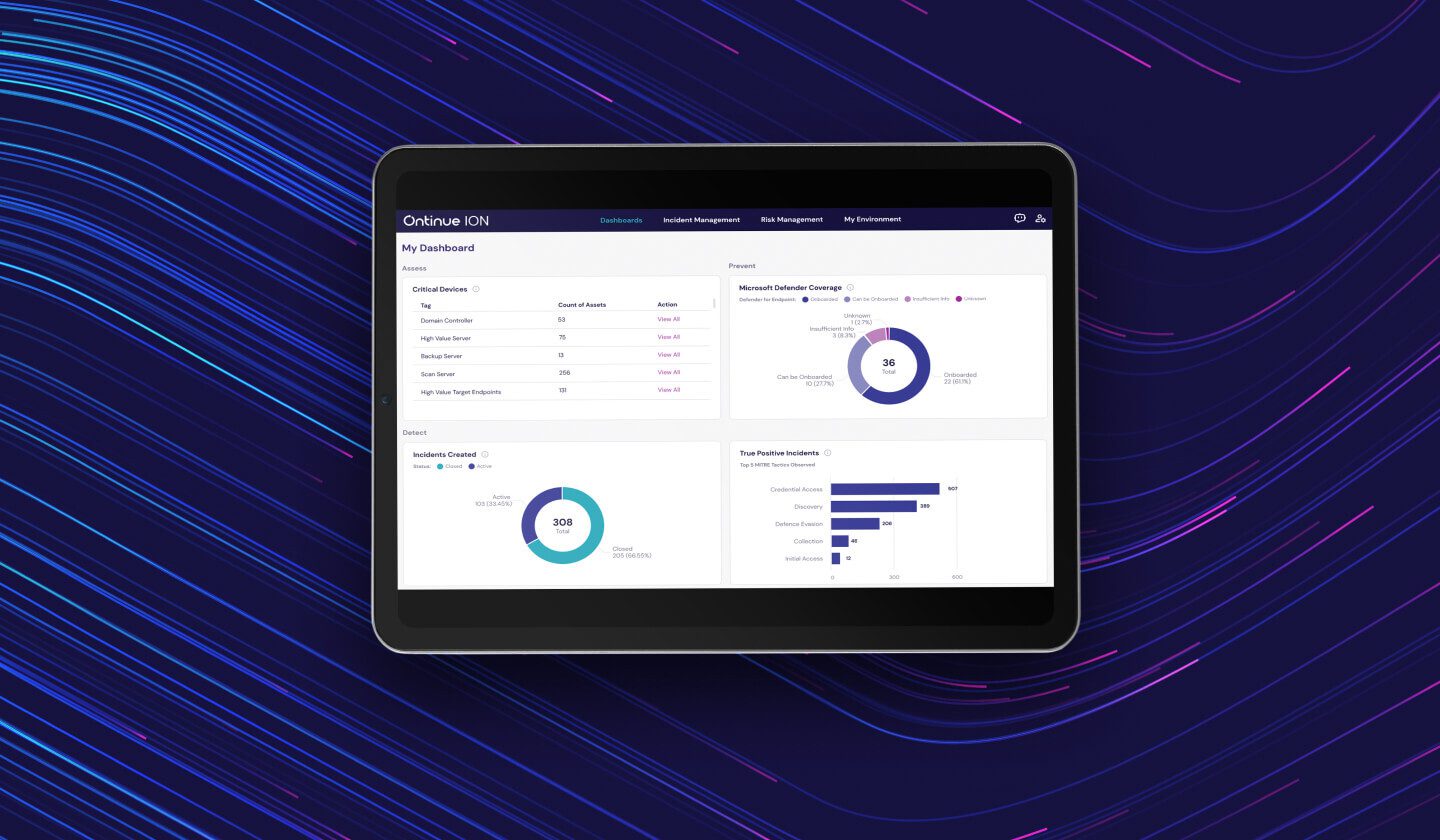
AI-POWERED DATA PLATFORM
We built our service on an AI technology platform that augments human intelligence to enable smarter, more precise communication, smoother teamwork, and transparency every step of the way.
Learn About Our Platform
24/7 SECOPS TEAM
Our experienced global security operations team is looking out for you 24/7. Wherever you are and whatever your security challenge is, we’re here to support the entire security lifecycle with threat hunting, intelligence, automation and engineering.
Learn About Our SOC
MICROSOFT SECURITY EXPERTS
Our Microsoft Security experts help you with deployment needs, best practices, hardening of your Microsoft security environment and improving your secure score to help eliminate threats to your business.
Learn About Our Consulting ServicesOntinue + Microsoft
As the 2023 Microsoft Innovation Partner of the Year and 2022 Microsoft Security MSSP of the Year, we understand Microsoft inside and out. That means we know how to help you implement and maximize your Microsoft security and collaboration tools.









The Ontinue Experience
Don’t just take our word for it. Here’s what customers have to say about their experience with Ontinue.
The Ontinue Difference
We don’t stop at detection and response; we’re an extension of your team. Together, we’ll build a proactive security operation that will continuously strengthen your security posture. Let’s win together.
LEARN MOREFaster, more consistent threat investigation and response, with quicker time to value.
AI combined with human expertise delivers faster, more precise, and comprehensive customized protection.
Microsoft Teams enhances collaboration by providing seamless access to human expertise and instantaneous access to information and insights.
With our focus and deep expertise in Microsoft Security, we help you optimize your tool stack, manage resource consumption, and maximize your Microsoft ROI.
AI that generates prioritized, actionable recommendations for improving security posture and preventing threats.
Unlike other MDR services, you can see our data usage, decision-making processes, and actions at any time.